Quick Answer: What Is a Spring IT Cleanup?
A spring IT cleanup is a proactive review of your business’s technology environment to identify hidden risks, improve cybersecurity, and ensure systems are reliable and recoverable.
It focuses on validating what’s already in place—rather than adding unnecessary complexity.
What Should Businesses Check First?
Start with these four areas:
- Backup and recovery: Can systems be restored quickly?
- Security monitoring: Are threats actively detected and responded to?
- User access: Does everyone have only the access they need?
- Visibility: Do you have clear insight into your network and systems?
These represent the most common points of failure in business IT environments.
Why a Spring IT Review Matters
Spring is a natural time to reset operations, improve efficiency, and prepare for growth.
But IT environments often evolve quietly over time—without regular review or validation.
This leads to gaps that aren’t obvious day-to-day, such as:
- Misconfigurations
- Outdated security settings
- Untested backups
- Over-permissioned users
Everything may appear to be working—until a disruption or security event exposes those gaps.
The Most Common Hidden IT Risks
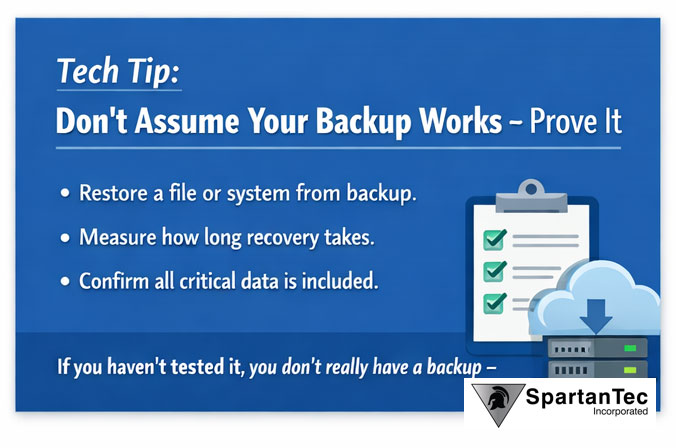
1. Backups That Haven’t Been Tested
Having backups is not the same as being able to recover from them.
Without testing, recovery failures often surface during critical moments.
2. Security Tools Without Active Monitoring
Many organizations have antivirus or endpoint protection in place—but lack continuous monitoring and response.
This leaves gaps in detecting modern threats.
3. Excessive or Outdated User Access
As organizations grow, access permissions accumulate.
Without review, this creates unnecessary exposure to sensitive systems and data.
4. Limited Visibility Across the Environment
Without centralized visibility, it becomes difficult to detect unusual behavior or respond quickly to incidents.
Spring IT Checklist for Businesses
To reduce risk and improve stability, review:
- Backup and disaster recovery processes
- Security monitoring and alert response
- User access and permissions
- System updates and patching
- Network and endpoint visibility
These foundational areas often provide the greatest improvement with the least disruption.
How Managed IT Services Improve Security and Stability
A managed IT provider helps businesses move from reactive to proactive by:
- Monitoring systems 24/7 for threats
- Maintaining security configurations and updates
- Providing visibility into system performance and risk
- Supporting users with reliable, responsive service
This approach reduces uncertainty and allows leadership to focus on business operations—not IT issues.
How Do You Know If Your IT Environment Is Secure?
A secure IT environment is one where leadership has confidence in:
- Detecting suspicious activity quickly
- Responding effectively to incidents
- Recovering systems without disruption
- Controlling and monitoring user access
If any of these areas are unclear, a review is recommended.
Final Thought: Confidence Over Complexity
Improving IT doesn’t require adding more tools.
In many cases, it’s about refining what’s already in place, closing gaps, and ensuring everything is working together effectively.
The goal isn’t perfection—it’s confidence.
If you’re unsure where your IT environment stands, SpartanTec can help.
We provide clear, practical insight into your current risk and what actually needs attention.
FAQ
How often should a business review its IT environment?
At least once per year, with continuous monitoring throughout the year.
What are the biggest hidden IT risks?
Untested backups, lack of monitoring, outdated configurations, and excessive user access.
Do I need to replace my IT systems to improve security?
No. Most improvements come from better configuration, monitoring, and processes.
What is included in an IT risk assessment?
Backup validation, security monitoring review, access control analysis, and visibility assessment.