For many organizations, information security compliance still feels like a task to complete rather than a discipline to maintain. Policies get written, boxes get checked — and then security quietly fades into the background.
That approach no longer works.
Today’s threat landscape, regulatory pressure, and business risks have made information security compliance a necessity, not a formality. Compliance is no longer about satisfying auditors; it’s about protecting your organization’s data, reputation, and ability to operate.
Compliance Has Changed — And So Have the Risks
Cyber threats have evolved far beyond basic malware and spam emails. Organizations now face AI-powered phishing and social engineering attacks, ransomware targeting backups and cloud systems, vendor and supply-chain breaches, insider threats, and regulatory penalties tied to data handling and privacy failures.
At the same time, compliance requirements have expanded. Frameworks such as HIPAA, PCI-DSS, SOC 2, state privacy laws, and industry mandates demand ongoing controls — not one-time documentation.
Why “Checkbox Compliance” Falls Short
Organizations that treat compliance as a checklist often discover gaps when it matters most. Policies exist but aren’t followed, controls are outdated, shadow IT goes unnoticed, and response plans are untested. When a breach happens, regulators and insurers don’t ask if you had a policy — they ask if you enforced it.
Compliance as a Business Enabler
When done correctly, compliance strengthens the business. It reduces cyber risk, builds trust, supports insurance requirements, and improves operational visibility. Compliance becomes a framework for smarter decision-making, not a burden.
What Effective Compliance Really Looks Like
True compliance is continuous. It aligns people, process, and technology through ongoing risk assessments, monitoring, training, testing, and governance.
Turning Compliance Into Protection
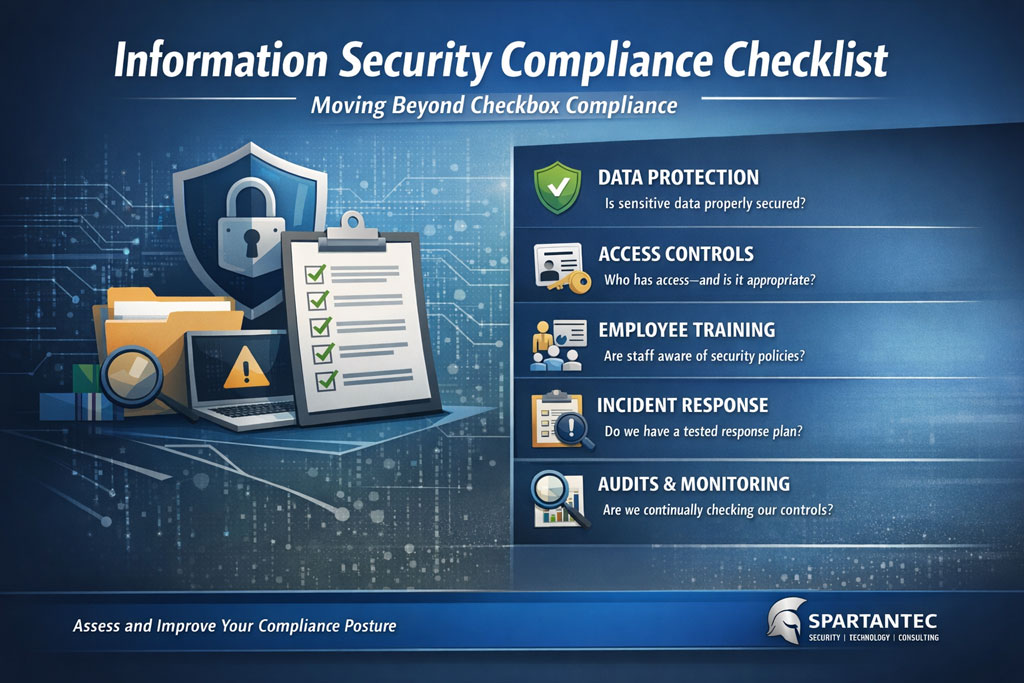
Organizations that succeed ask the right questions: Do we know where our data lives? Who has access? Are we prepared for incidents? Can we demonstrate our controls are working?
Start the Conversation
If you’re unsure whether your current compliance efforts reflect your real-world risks, a short conversation can bring clarity. SpartanTec also offers a practical Information Security Compliance Checklist to help organizations identify gaps and prioritize next steps.